-
Notifications
You must be signed in to change notification settings - Fork 14
Home
Use at your own risk!
**_See in action:_**
$ ./cnc1_test.py: + registers the local computer as Standard Proxy, that can be visible on the available proxy list, i.e. in VIP72 panel + works in an infinite loop, resending beacon after every 10 minutes to keep connection alive
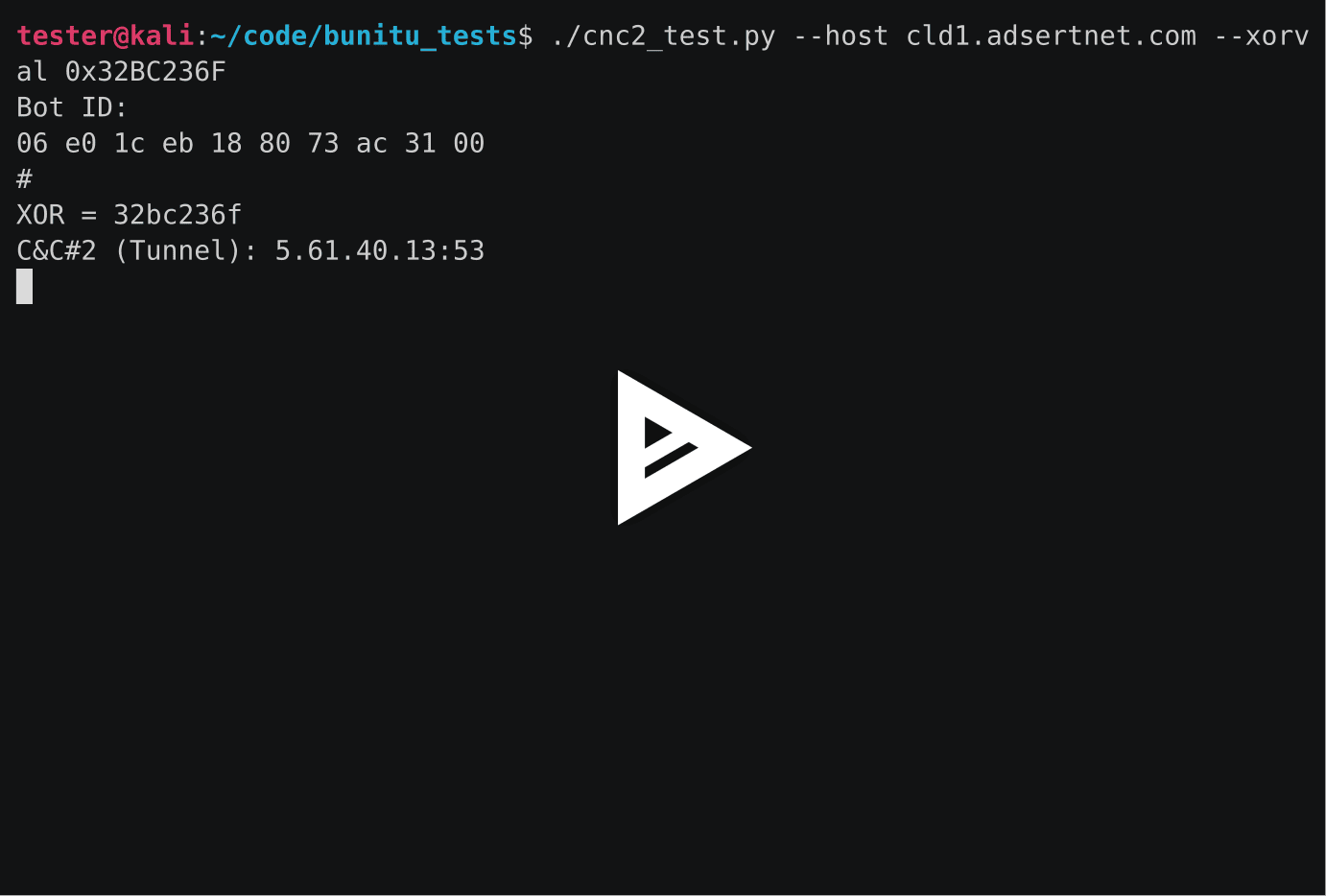
$ ./cnc2_test.py: + registers the local computer as Tunneled Proxy + receives initial testing request and displays it
**_Files:_**
- cnc1_test.py - registers your host as a proxy bot in the Bunitu botnet (communicate with C&C#1)
- cnc2_test.py - checks if the given host is a Bunitu Tunneling C&C (communicate with C&C#2)
- bunitucommon.py - set of common functions for scripts to communicate with bunitu C&Cs
- util.py - set of general utility functions for scripts to communicate with bunitu C&Cs
_**Constants:**_
util.py:
REBOOT_TIME = 1434924029619 # (arbitrary chosen) fake time of last
# system reboot in millisec
cnc1_test.py:HOST_1 = 'ns3.joinparty4beer.xyz' # hardcoded in the sample:
# b71832a8326b598208f49bf13e5b961f
PORT_1 = 53 # typical for Bunitu
MALWARE_VERSION = 0xf0b9 # hardcoded in the sample:
# b71832a8326b598208f49bf13e5b961f
XORVALUE = 0x16ec1a31 # value used in calculation of C&C IP,
# may be different for different version
HARD_TICKS = 0x67701bf6 # arbitrary chosen value
TIMEOUT = 1
cnc1_test.py:VERBOSE = False
TUNNEL_HOST = 'ns1.joinparty4beer.xyz # hardcoded in the sample:
# b71832a8326b598208f49bf13e5b961f
PORT_1 = 53 # typical for Bunitu
MALWARE_VERSION = 0xf0b9 # hardcoded in the sample:
# b71832a8326b598208f49bf13e5b961f
XORVALUE = 0x16ec1a31 # value used in calculation of C&C IP, may be
# different for different version
TIMEOUT = 3
_**Options:**_
./cnc1_test.py --help
usage: cnc1_test.py [-h] [--id NEW_ID] [--genid] [--once] [--ip CNC_IP]
[--host CNC_HOST] [--port CNC_PORT] [--xorval CNC_XORVAL]
This script can be used to register your host as a proxy in the Bunitu botnet.
optional arguments:
-h, --help show this help message and exit
--id NEW_ID Specify a new bot id to use. This must be a binary
string. Use the --genid command to generate one.
--genid Generate a new bot id string and quit.
--once Only send one request. The default is to repeatedly
send requests ever 10min to mimic the real bot.
--ip CNC_IP C&C (explicit) IP
--host CNC_HOST C&C Host (alternative for explicit IP, use internal
algorithm to get C&C IP),
default=ns3.joinparty4beer.xyz
--port CNC_PORT C&C port, default=53
--xorval CNC_XORVAL XOR value used to resolve C&C IP, default=384571953
(0x16ec1a31)
./cnc2_test.py --help
usage: cnc2_test.py [-h] [--id NEW_ID] [--genid] [--verbose] [--host CNC_HOST]
[--ip CNC_IP] [--port CNC_PORT] [--xorval CNC_XORVAL]
[--timeout CNC_TIMEOUT]
This script can be used to register your host as a proxy in the Bunitu botnet.
optional arguments:
-h, --help show this help message and exit
--id NEW_ID Specify a new bot id to use. This must be a binary
string. Use the --genid command to generate one.
--genid Generate a new bot id string and quit.
--verbose Deploy script in verbose mode.
--host CNC_HOST C&C Host (alternative for explicit IP, use internal
algorithm to get C&C IP),
default=ns1.joinparty4beer.xyz
--ip CNC_IP C&C (explicit) IP
--port CNC_PORT C&C port, default=53
--xorval CNC_XORVAL XOR value used to resolve C&C IP, default=384571953
(0x16ec1a31)
--timeout CNC_TIMEOUT
Timeout fot C&C response, default=3
_**Usage Examples:**_
./cnc1_test.py
The script sends the registration request in a loop, to keep the host registered in C&C#1:
$ ./cnc1_test.py Bot ID: 05 38 99 82 13 e0 64 0a 26 c0 # C&C#1: 62.212.66.85:53 time since rebooot: 4:4 REQUEST: 00 01 01 00 00 01 00 00 00 00 00 00 67 ab a0 32 05 00 04 04 05 38 99 82 13 e0 64 0a 26 c0 00 00 00 00 00 00 b9 f0 00 00 00 00 00 00 sent! response len: 0 time since rebooot: 4:14 REQUEST: 00 01 01 00 00 01 00 00 00 00 00 00 67 ab a0 32 05 00 0e 04 05 38 99 82 13 e0 64 0a 26 c0 00 00 00 00 00 00 b9 f0 00 00 00 00 00 00 sent! response len: 0 [...]
./cnc2_test.py
The script sends the registration request once, and waits for the response of the remote server. If the remote server is a Bunitu Tunnel (C&C#2) it responds by the internal protocol (asks the bot to check connection with Google).
The script returns True in a case, if the response of the server follows the Bunitu protocol, False otherwise.
$ ./cnc2_test.py Bot ID: 03 60 13 af 0b 80 4d bc 17 00 # C&C#2 (Tunnel): 95.211.178.145:53 RESPONSE, len: 75 2e 00 00 00 03 60 13 af 00 00 00 00 00 00 00 00 00 00 00 00 01 00 00 01 00 00 00 00 00 00 00 00 bc 79 ab 3f 01 67 6f 6f 67 6c 65 2e 63 6f 6d 00 50 00 15 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 05 ff ff ff ff LEN : 2e = 46 LEN : 15 = 21 Packages: 2 > DNS_QUERY: google.com True echo $? 1Boths scripts can be deployed with a specific bot ID, i.e:
./cnc2_test.py --id \x06\xf8\xbf\x42\x16\xe0\xff\x0a\x2c\xc0 Bot ID: 06 f8 bf 42 16 e0 ff 0a 2c c0 # [...]The Bot ID can be generated by the script, deployed with appropriate parameter:
./cnc2_test.py --genid \x06\xf8\xbf\x42\x16\xe0\xff\x0a\x2c\xc0