introduce F2B v0.11#1965
Conversation
|
@casperklein Although unit tests fail, it is only one tests, which is version related: Can you have a look? |
|
@docker-mailserver/maintainers If someone is not fine with getting the latest Fail2Ban, please share your concerns here :) |
If it doesn't solve the issue discussed in #1810 and still needs the "hacking" i see no real benefit. If there is an advantage then go for it (imho) |
|
@wernerfred You right: I think that
is one good arguments. The other one may be that we should be at the forefront of security. I like having the latest versions :D |
| razor rpm2cpio rsyslog sasl2-bin spamassassin supervisor \ | ||
| unrar-free unzip whois xz-utils >/dev/null && \ | ||
| # Fail2Ban | ||
| curl -Lso fail2ban.deb https://github.com/fail2ban/fail2ban/releases/download/0.11.2/fail2ban_0.11.2-1.upstream1_all.deb && \ |
There was a problem hiding this comment.
If we do this to be on forefront of security then we should check the downloaded files integrity/signing shouldn't we?
There was a problem hiding this comment.
Yes, we should do that. Can you help? Not sure what's the best solution, I mean, how to check this. The release page of F2B offers a link to check a hash sum.
There was a problem hiding this comment.
One easy method, without using GPG, would be to check the pre-computed SHA152 sum like this:
sha512sum --check --status <<< "09d91ad0f499b0825b9d6da1d175400aa32498aff5705624e88b3d7e02cf727403c49b967c732e42182e25d4f439de0faf681f9f6d3598364e3f2f2e3453f8bf fail2ban_0.11.2-1.upstream1_all.deb"which could be written directly into the Dockerfile. Moreover, sha512sum is from the coreutiles package - no extra package dependency necessary. The downside is: just an integrity check, no signature verification.
There was a problem hiding this comment.
This should be enough, to ensure the file was not altered.
However, my checksum differs:
echo "44fe3d67e7d24bba4fc81ee672059dcb67980258db6101bcd8740736a9d9110f *fail2ban.deb" | sha256sum --check --status
or
sha256sum --check --status <<< "44fe3d67e7d24bba4fc81ee672059dcb67980258db6101bcd8740736a9d9110f *fail2ban.deb"
There was a problem hiding this comment.
Is there a reason for the package pinning in that particular case
no just personal habit ;) sorry
IMO we don't need FAIL2BAN_VERSION at all. There are not that much releases of f2b. And as you said, when there is a new version, we have to adjust the Dockerfile and maybe f2b_url either way.
Agree 👍🏻
In context of security, this feels wrong: wget -q --no-check-certificate.
True but doesn't matter if the signing is correct. There is no need to use wget, we can also use curl if that does behave other than wget in CI. If you look at the linked example in my comment above i do not use --no-check-certificate and have no issues with gh action or am i missing smth?
What kind of improved security do we get from this, compared to the very simple file hash comparison
We are not only checking if the file got altered but also if it was created by fail2ban or did i get it wrong?
Nevertheless the hash comparison adds that bit of security compared to having no check at all that i am fine with both ☑️
ARG should be ENV
I disagree as we have no benefit of having these as ENV in the Container later on. We only need them during build an therefore ARG should be enough. But as the behavior does not change i do not insist of using ARG
There was a problem hiding this comment.
We are not only checking if the file got altered but also if it was created by fail2ban or did i get it wrong?
Correct. I considered this only as a temporary addition (until Debian 11 is released). So manually sign checking once and then hard-coding the checksum would be enough (way less additions to Dockerfile needed).
If we are going this route long-term, then the gpg solution is more complete and convenient 👍
We only need them during build an therefore ARG should be enough.
Good point. I had the wrong assumption, that using ARG in Dockerfile and not providing a build-arg for that during the build would throw a warning. That is not the case.
Maybe we should think about replacing most ENV with ARG in the whole Dockerfile. The ENVs are populated by the start-mailserver.sh script. So we don't need to bake them into the image.
There was a problem hiding this comment.
The ENVs are populated by the start-mailserver.sh script. So we don't need to bake them into the image.
Good point
 wernerfred
left a comment
wernerfred
left a comment
There was a problem hiding this comment.
I suggested changes to drop the FAIL2BAN_VERSION and removed the version pinning of packages
Co-authored-by: Frederic Werner <[email protected]>
Co-authored-by: Frederic Werner <[email protected]>
Co-authored-by: Frederic Werner <[email protected]>
Co-authored-by: Frederic Werner <[email protected]>
|
@casperklein @wernerfred I'm low on time today and tomorrow (Bachelor's thesis is waiting for me). Can you take care of the changes you suggested. I'm more than happy to review this in the end. |
|
LGTM Anything left to do? |
 wernerfred
left a comment
wernerfred
left a comment
There was a problem hiding this comment.
I think this is fine to merge.
Do we need a documentation Update?
I don't think docs needs an update. I will go ahead and merge this. |
|
Not doc, but we should mention it in the changelog as a breaking change, when v10 will be released. |
|
I just wondered, why there is no new image @ dockerhub. --> |
|
Do we have an arch problem? |
|
Yes. But what exactly goes wrong is hard to tell, because all error output is suppressed. |
|
What are the next steps? How to debug this? Should we open a PR after #1970 got merged to see the build output on arm or do we revert this PR? |
|
#1970 does not add additional output. It will only help for future PRs, so that we know in advance before merging, the build fails. To get more output and track down which command exactly fails, we would have to remove all the I did this locally, but unfortunately, my build for arm64/armv7 both succeed. I looked for the "exit code 60" in google and the first result was about a certificate problem of curl. @aendeavor mentioned:
If I had to blindly guess, I would say, that curl behaves similar. To track down this and future problems more easily, it's probably a good idea, to remove the |
That is probably it.
Yes. |
|
I can try to adjust @wernerfred @aendeavor if one of you could do it, I wouldn't be sad 😘 Or do you have any other suggestions how to proceed? |
Still low on time to be honest 🙈 I have not done the build stuff at all. But I will help if I can. Remember, we've got time, no need to hurry. |
|
I had a look and will give it a try. Doesn't seem that hard as I thought. Edit: See #1972 |
But why does it work in the PR test then? This run is also in CI environment. Strange |
|
Good point. That would indicate it's just related to arm builds? Or the curl guess is wrong. |
We can still revert #1965 and restore the |
|
When #1972 passes on |
|
Absolute, will have the Same result. Just a Point of having a broken state commited to master for a certain amount of time |
I can live with that, since |
|
Another downside of the Line 54 in 225e21e |
This new script is a clean way of handling the installation of packages. I think the huge `RUN` command in `Dockerfile` was hard to read and maintain. Using a script is a non-issue, as the image is rebuilt whenever the script is touched. Moreover, this commit implicitly removed the explicit Fail2Ban installation and therefore #1965, BECAUSE Debian 11 now ships with the latest and greatest Fail2Ban version (even more up-to-date than out current version it seems).
Description
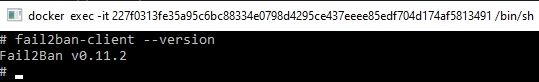
This PR replaces F2B 0.10 with the latest F2B 0.11.2. This is done as Debian 11 has still no ETA. This change is easily revertible. When Debian 11 launches with the latest F2B, this PR can be reverted in a manner of minutes.
Fixes #1810
Type of change
Checklist:
docs/)