Shiro security v2#586
Shiro security v2#586hayssams wants to merge 14 commits intoapache:masterfrom ebiznext:shiro-security-v2
Conversation
Websocket security is done in the next commit
|
@hayssams Can you provide step-by-step directions for configuring and using this? |
Step 1: Require HTTP AuthIn conf/shiro.ini file, replace the lines 31 and 32 below by Step 2: Secure the Websocket channelRename the conf/zeppelin-site.xml.template to conf/zeppelin-site.xml. Step 3: Start Zeppelin and AuthenticateTo authenticate, use one of the user/password set in the conf/shiro.ini file. See below I've also included a SECURITY-README file in the PR. |
|
I tested this PR, and it does ask for basic auth credentials after setting up However, after login, it does not show the Zeppelin welcome page as expected. (you can however navigate to specific notebooks). |
|
What is the purpose of ticket? And why do you save principal and ticket in the notebook? What will happen to my notebook if i have zeppelin and update to use it with shiro and viseversa? |
…lt in zeppelin-site.xml.template
|
@jeffsteinmetz |
Question 1 : What's the purpose of ticket ?I added an implementation note in the security-readme file. It explains why we need a ticket to handle webscoket connections. Basically, it works as follows :
Question 2 : Ticket saved in notebook ?In this PR( #586) Principal and ticket are not saved in the notebook. Question 3 : What will happen if switching from secure to non secure version and vice-versaIn this PR( #586). It will work as expected since no change is made to the notebook structure. |
|
Confirmed: Welcome page is now correctly displayed. |
|
Follow up question: Is it the responsibility of shiro to redirect to SSL so that the basic auth is not sent in the clear? I saw shiro this example:
|
|
@hayssams Thanks for the v2 branch. I'm having some error with zeppelin-web development mode could you take a look? |
|
@jeffsteinmetz |
|
@Leemoonsoo P.S. I am using |
|
@hayssams Makes sense. I could give the SSL redirect a test, and use the SSL support already exposed by Zeppelin. |
|
@Leemoonsoo |
|
@Leemoonsoo |
|
@hayssams Thanks, confirmed the last commit made zeppelin-web dev mode work. However, if shiro.ini is configured to use authcBasic, zeppelin-web dev mode still does not work correctly. Could you take a look once again? |
|
@Leemoonsoo |
|
@hayssams Thanks, zeppelin-web dev mode works well. About CI build, Do you see any reason for the failing? |
|
@Leemoonsoo |
bin/zeppelin.sh
Outdated
There was a problem hiding this comment.
Is there a special reason adding $ZEPPELIN_CONF_DIR/shiro.ini: in this line?
There was a problem hiding this comment.
Since shiro loads the first shiro.ini file in the classpath. I've put here so that the one in the conf directory is loaded.
There was a problem hiding this comment.
ZEPPELIN_CONF_DIR is already in the classpath. I think it shiro loads shiro.ini without this modification. Could you confirm?
There was a problem hiding this comment.
Yes you are right. This reference to shiro.ini in the classpath is useless.
|
@hayssams Great to see CI test passing! You'll also need to update https://github.com/apache/incubator-zeppelin/blob/master/zeppelin-distribution/src/bin_license/LICENSE for And could you explain little bit about how |
|
@Leemoonsoo |
|
@hayssams Thanks for explain about auth mode. Looks good to me |
|
@Leemoonsoo |
|
Merge if there're no more discussions |
|
@Leemoonsoo |
### What is this PR for? hayssams Leemoonsoo Just tested #586 with a local LDAP, works well for me. Included a sample config. ### What type of PR is it? Documentation / Sample testing. ### How should this be tested? Change configs to point to a local/available LDAP, uncomment the parameters, replacing the individual values. Author: Rohit Choudhary <[email protected]> Closes #625 from rconline/SHIRO_LDAP and squashes the following commits: fa0b69c [Rohit Choudhary] Enabling annonymous access, commenting out AuthBasic. ead38fd [Rohit Choudhary] Tested with local LDAP configurations.
### What is this PR for? About a month ago, Shiro authentication for Zeppelin is merged by #586. Even though we already have [SECURITY-README.md](https://github.com/apache/incubator-zeppelin/blob/master/SECURITY-README.md), many people do not know about the existence of this file. So I wrote a docs based on `SECURITY-README.md` to the Zeppelin documentation website to guide step by step for Zeppelin users. ### What type of PR is it? Documentation ### Todos * [x] - Add shiro authentication docs * [x] - Add **zeppelin.anonymous.allowed** property in `zeppelin-site.md` * [x] - Indent **Websocket security** section in `SECURITY-README.md` ### Is there a relevant Jira issue? [ZEPPELIN-661](https://issues.apache.org/jira/browse/ZEPPELIN-661) ### How should this be tested? ### Screenshots (if appropriate)  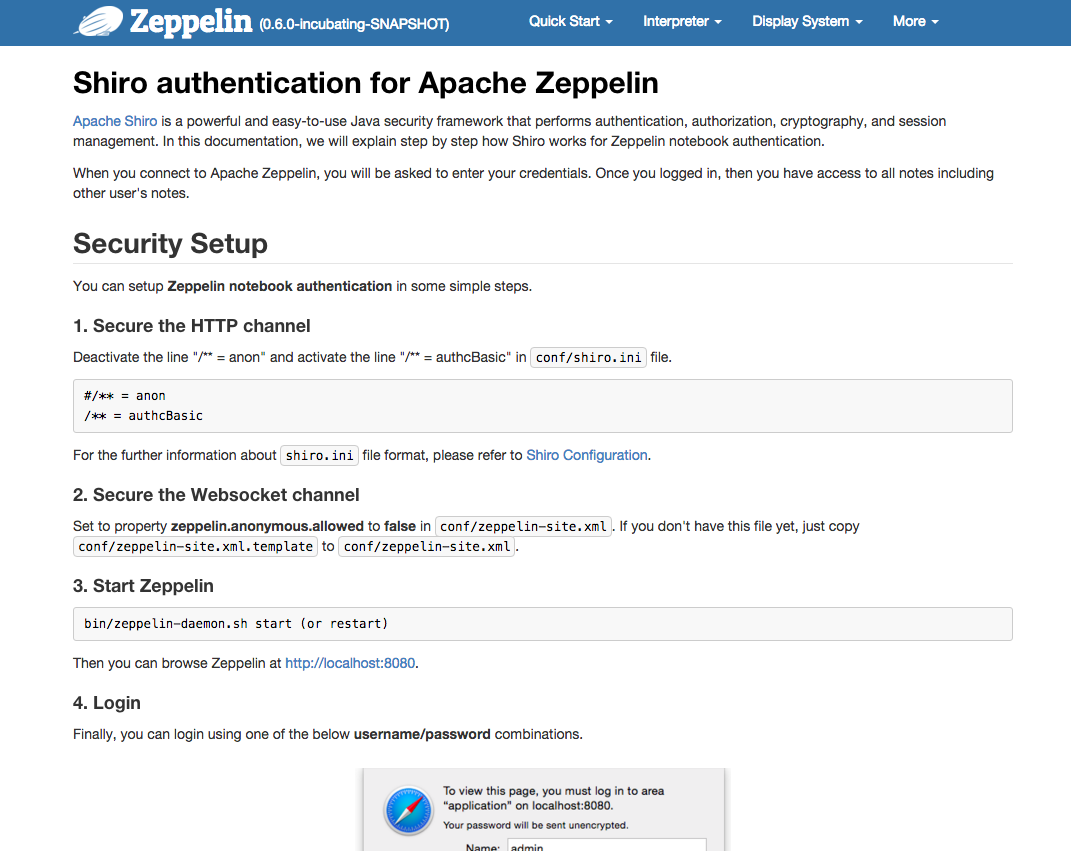 ### Questions: * Does the licenses files need update? No * Is there breaking changes for older versions? No * Does this needs documentation? No Author: Ryu Ah young <[email protected]> Closes #711 from AhyoungRyu/ZEPPELIN-661 and squashes the following commits: 482fc65 [Ryu Ah young] ZEPPELIN-661: ping travis 4fbc5e5 [Ryu Ah young] ZEPPELIN-661: Add the default status information of anon and authcBasic 795f177 [Ryu Ah young] ZEPPELIN-661: indent 'Websocket security' section in SECURITY-README.md f050f8d [Ryu Ah young] ZEPPELIN-661: Add 'zeppelin.anonymous.allowed' property in zeppelin-site.xml to install.md d841a8a [Ryu Ah young] ZEPPELIN-661: Add shiro authentication docs
### What is this PR for? The goal of the PR is to pass userName/userInfo from front-end to interpreters. The PR uses Shiro authentication(#586). ### What type of PR is it? Improvement ### Todos * [x] - Change RemoteInterpreterService.thrift signature * [x] - Change InterpreterContext/RemoteInterpreterContext signature * [x] - Modify all existing interpreters to above signature ### Is there a relevant Jira issue? N/A Author: Prabhjyot Singh <[email protected]> Closes #705 from prabhjyotsingh/UserInInterpreterContext and squashes the following commits: 563d43f [Prabhjyot Singh] CI fix, missed earlier f084994 [Prabhjyot Singh] Merge remote-tracking branch 'origin/master' into UserInInterpreterContext 3c979d2 [Prabhjyot Singh] fixing CI failure 033a354 [Prabhjyot Singh] Merge remote-tracking branch 'origin/master' into UserInInterpreterContext e4a5165 [Prabhjyot Singh] move AuthenticationInfo from dispaly package to user 0709b9c [Prabhjyot Singh] moving AuthenticationInfo to org.apache.zeppelin.display.AuthenticationInfo 95e7c13 [Prabhjyot Singh] test for selenium a5a991d [Prabhjyot Singh] check for selenium 34dcc32 [Prabhjyot Singh] instead of null pass "new AuthenticationInfo()" ba91da4 [Prabhjyot Singh] Merge remote-tracking branch 'origin/master' into UserInInterpreterContext 57ca577 [Prabhjyot Singh] review change create such class AuthenticationInfo, and pass it into InterpreterContext 320790c [Prabhjyot Singh] fix for CI, missing change signature d928203 [Prabhjyot Singh] revert shiri.ini if fromMessage.principal.equals("anonymous") then set user as null fadc6d9 [Prabhjyot Singh] userName to be present in InterpreterContext/RemoteInterpreterContext

Added Authentication.
Once authenticated, a user has access to all notes.
HTTP & Websocket channels are secured and require auth.
This PR is based on #53 which also implements user ownership on notes.