added
Inbound SCIM Groups for Enterprise Connections is now Generally Available!
We’re pleased to announce that support for Groups within Auth0’s Inbound SCIM for Enterprise Connections capability is now Generally Available (GA)!
This release closes the loop between identity provisioning and access control by allowing you to natively map synced groups to Auth0 roles at two levels: globally at the tenant level, or scoped specifically to an organization based on the user’s login context.
Additionally, developers can now accelerate B2B onboarding by empowering their enterprise customers to self-configure SCIM provisioning for groups directly.
What’s new in GA:
Building on our Early Access capabilities, this release introduces the following enhancements to deliver out-of-the-box B2B delegated administration:
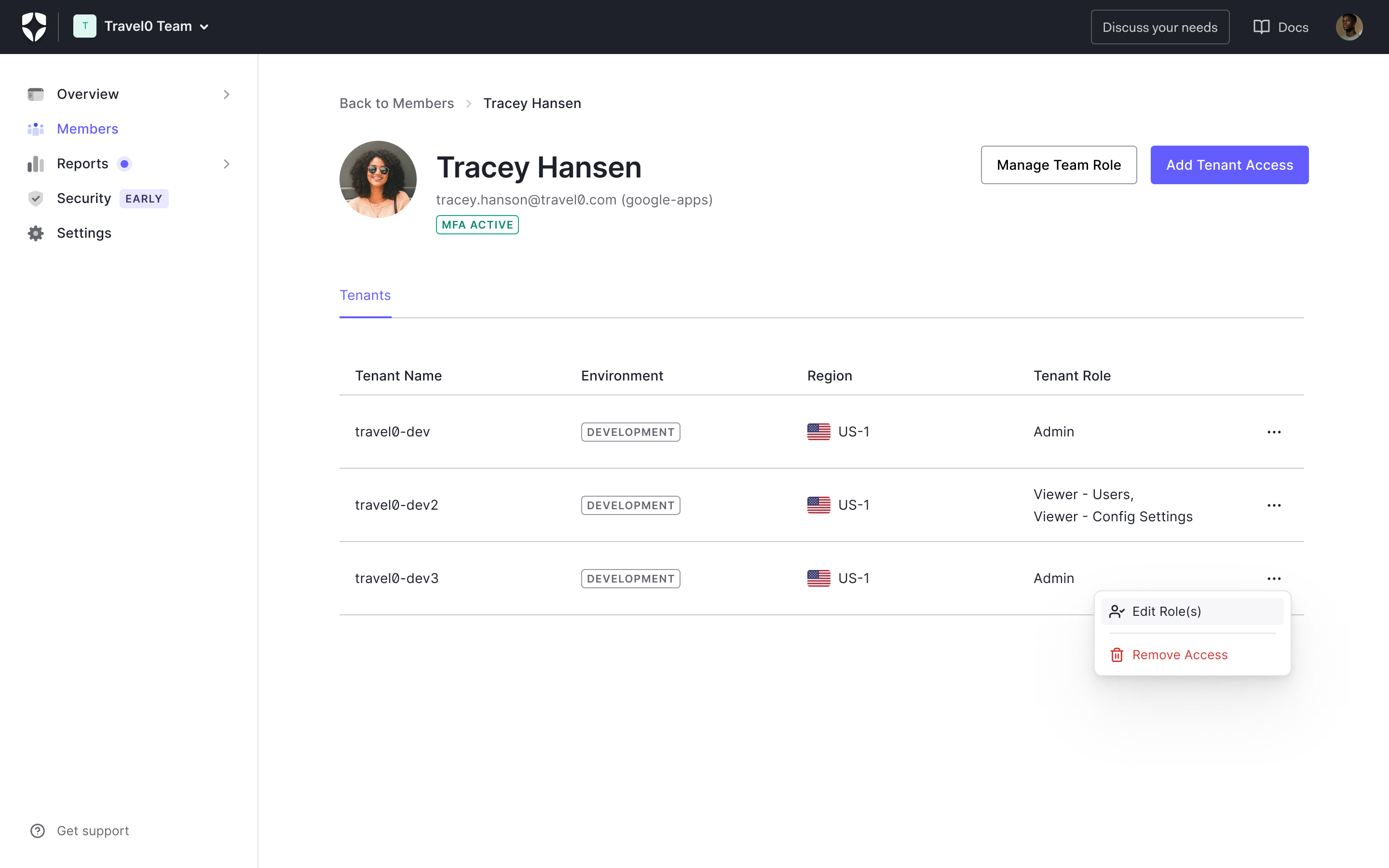
- Associate tenant-level RBAC roles with Enterprise Groups: For global access, you can assign Auth0 tenant-level roles directly to SCIM-provisioned groups. Any member of the synced group will automatically inherit these roles globally.
- Assign Organization scoped roles to Enterprise Groups: You can now assign organization scoped roles to SCIM-provisioned groups. In tandem with Auto-Membership, your customers' users will automatically inherit workspace-scoped permissions the moment they log in.
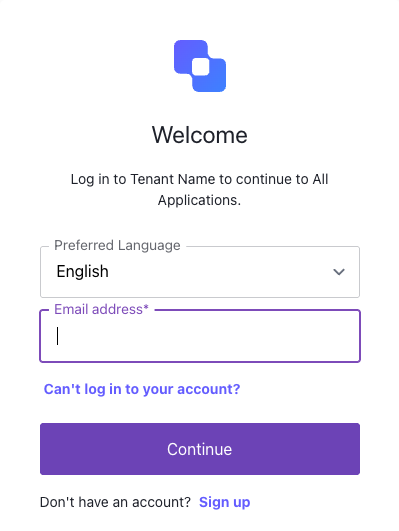
- Self-Service Enterprise Configuration: Empower your enterprise customers (or their IdP administrators) to configure SCIM provisioning for users and groups on their own through the Self-Service flow, accelerating B2B onboarding and removing your support team from the loop.
How to get started:
This feature will be rolled out to all public cloud environments over the next few days and to private cloud environments as per their release pipeline.
SCIM Groups is available for all tenants whose Auth0 plan includes Enterprise Connections. To enable it, navigate to the Auth0 Dashboard, go to Authentication > Enterprise, select your SAML, OpenID Connect, Okta Workforce, or Microsoft Entra ID connection, and toggle Sync user profiles using SCIM to On under the Provisioning tab.
Learn more: